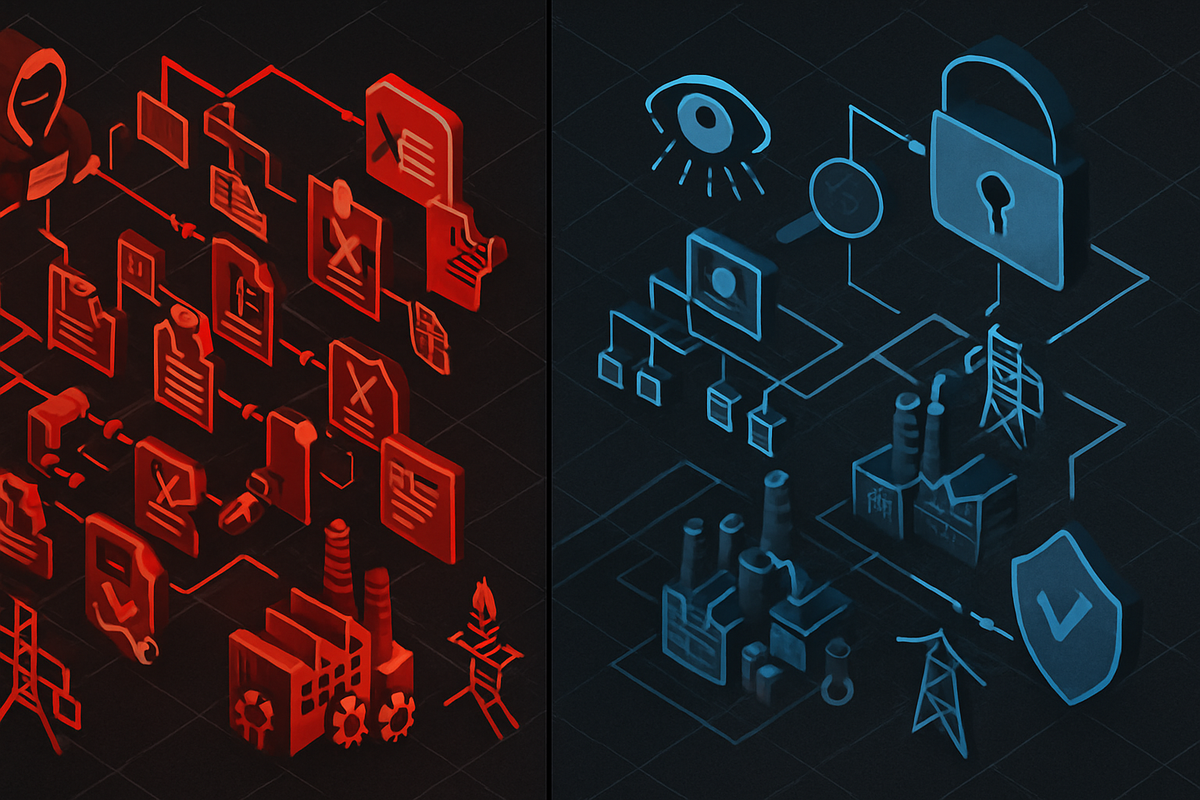
The threat to critical infrastructure has changed. Has your readiness?
Five-year dwell times and living-off-the-land techniques have changed what critical infrastructure readiness means. Here's what actually closes the gap.
In February 2024, CISA and the FBI confirmed what investigators had been piecing together for years: Volt Typhoon, a China-sponsored threat actor, had been inside U.S. critical infrastructure networks for at least five years before anyone noticed. Energy. Communications. Water. Transportation. The adversary wasn't stealing data. It was waiting.
That changes what readiness means.
The adversary is already inside
The old threat model assumed opportunistic attackers: criminals after financial gain, nation-states after intellectual property. Detection programs were built around data exfiltration. Incident response plans were calibrated for breaches measured in days or weeks.
Volt Typhoon doesn't fit that model. Microsoft's threat intelligence team documented the group's objective as disruption capability: pre-positioning inside critical systems to enable future operational disruption at a time of China's choosing. Not now. When conditions are right. The access is the weapon, held in reserve.
I've seen this framing dismissed as geopolitical sensationalism. The Sandworm record makes it hard to dismiss. In both the 2015 and 2016 Ukraine power grid attacks, Sandworm gained initial access through corporate IT, mapped its way to SCADA systems reachable from that network, and executed. The 2022 deployment of Industroyer2 against Ukrainian energy infrastructure confirmed the pattern: the malware was pre-staged before the February invasion. The dwell-to-activate cycle is not theoretical. It is documented.
If five-year dwell is real, quarterly threat hunting cycles and annual IR plan reviews are not running at the adversary's tempo. They're running at a tempo the adversary accounted for long ago.
Why your current posture may be working against you
Two structural assumptions are baked into most critical infrastructure security programs. Both have been invalidated.
The first is that signature-based detection will catch intruders. Volt Typhoon specifically avoided introducing custom malware. The documented tool list reads like a Windows administration manual: wmic, netsh, ntdsutil, PowerShell, Certutil, RDP. Enterprise EDR treats all of them as normal activity because they are normal activity when used by administrators. The adversary counted on that. Detection requires behavioral baselining and anomaly analysis, not signature matching against known-bad hashes.
The second assumption is that the IT/OT boundary protects OT systems from IT-side intrusions. It doesn't, and it hasn't for years. Remote access expansion punched holes in previously isolated OT networks. Data historians bridge OT process data to enterprise analytics platforms. Vendor credentials and engineering workstation connections provide bidirectional network paths that bypass DMZ controls. The Purdue model's hard boundary is a design document, not a description of most production environments.
Colonial Pipeline comes up constantly as a critical infrastructure attack. It wasn't, exactly. DarkSide ransomware infected IT systems; Colonial shut down OT pipeline operations voluntarily as a precaution. The OT systems weren't directly compromised. That's actually more instructive than if they had been: an IT event caused operational disruption without the adversary ever touching the pipeline controls. A threat model built on "they want our data" is structurally misaligned to "they want the ability to turn off our systems." That holds even when the path into disruption runs entirely through IT.
Three controls that actually close the gap
Three controls address the specific failure modes that current adversary TTPs exploit. None require starting over.
Network traffic analysis with OT protocol awareness
OT devices can't run endpoint agents, and LOTL techniques evade EDR. The detection layer has to live on the wire. Passive NTA tools with coverage for Modbus, DNP3, EtherNet/IP, and PROFINET are the minimum viable detection capability for OT-adjacent networks. If your visibility ends at the IT layer, your detection ends there too. That is precisely where the adversary is heading.
Zone-and-conduit segmentation, actually enforced
ISA/IEC 62443's zone-conduit model reduces the blast radius of lateral movement from IT into OT. The word "enforced" is doing real work in that sentence. Paper segmentation doesn't stop an adversary who is already inside. Every IT-to-OT path needs a defined conduit with explicit allow-list rules: vendor remote access, data historian feeds, and engineering workstation connections are the common paths requiring their own. Not a broad firewall policy with implicit deny. Explicit allow-listing, reviewed and kept current.
Threat hunting that reads OT
Enterprise hunters don't know what normal looks like in an OT environment, and that gap is the problem. Effective hunting in OT-adjacent networks requires baselines for engineering workstation behavior, vendor access schedules, PLC programming cycle patterns, and OT protocol traffic volumes. A PLC programming change outside a maintenance window is the OT equivalent of a domain admin account logging in at 2 AM. It's only visible to hunters who know what they're looking for.
When did you last update your threat models against current adversary behavior? When did you last test whether your detection chain extends past the IT/OT boundary?
CISA's Cross-Sector Cybersecurity Performance Goals are a useful floor: asset inventory, network segmentation, MFA for remote access, revoked credentials for departed employees. If your organization operates in or adjacent to a sector named in the Volt Typhoon advisories, CPG compliance is where you start, not where you stop.
The adversary has been patient. Most readiness programs haven't matched that patience. That is not a criticism of anyone's team. It is an audit item. The gap is documented and closeable. But only if the audit is honest about whether your current posture was built for the threat that exists now, or the one that existed three years ago.
Sources
- Volt Typhoon targets US critical infrastructure with living-off-the-land techniques — Microsoft Threat Intelligence, May 2023
- People's Republic of China State-Sponsored Cyber Actor Living off the Land to Evade Detection (AA23-144A) — CISA / Five Eyes joint advisory, May 2023
- PRC State-Sponsored Actors Compromise and Maintain Persistent Access to U.S. Critical Infrastructure (AA24-038A) — CISA / Five Eyes joint advisory, February 2024
- Analysis of the Cyber Attack on the Ukrainian Power Grid — E-ISAC and SANS ICS, March 2016
- ESET Research Exposes Industroyer2 — ESET Research, April 2022
- DarkSide Ransomware: Best Practices for Preventing Business Disruption (AA21-131A) — CISA / FBI joint advisory, May 2021
- NIST SP 800-82 Rev. 3: Guide to Operational Technology (OT) Security — NIST, September 2023
- Cross-Sector Cybersecurity Performance Goals — CISA
- MITRE ATT&CK for ICS
- M-Trends 2024 — Mandiant / Google Cloud
Revision History
2026-04-14 — published
Initial Publish
Comments ()